April 6, 2026
Axios npm Supply Chain Attack — How Hackers Poisoned v1.14.1 and Compromised 100M Developers
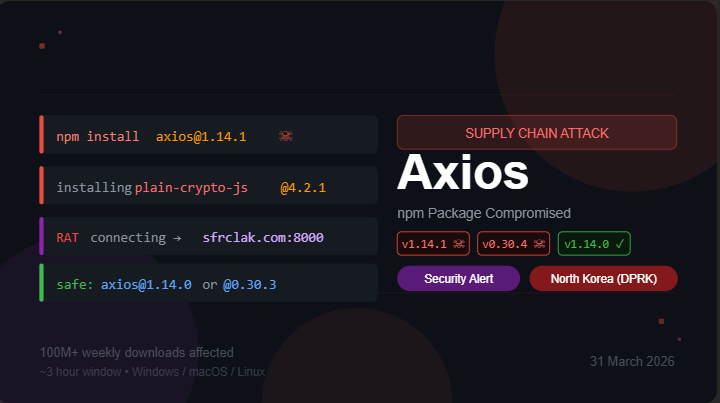
On March 31, 2026, attackers hijacked an Axios maintainer account and injected a Remote Access Trojan into versions 1.14.1 and 0.30.4. Within a 3-hour window, millions of developers worldwide were at risk — without changing a single line of their own code.
Here's the complete blog content in English — copy-paste ready for each field:
📌 TITLE
Axios npm Supply Chain Attack — How Hackers Poisoned v1.14.1 and Compromised 100M Developers📌 EXCERPT
On March 31, 2026, attackers hijacked an Axios maintainer account and injected a Remote Access Trojan into versions 1.14.1 and 0.30.4. Within a 3-hour window, millions of developers worldwide were at risk — without changing a single line of their own code.📌 CONTENT
H1 → Axios Supply Chain Attack: What Happened, How It Worked, and What You Should Do
March 31, 2026 was a wake-up call for the entire JavaScript community. Axios — one of the most trusted HTTP client libraries in the npm ecosystem — was compromised in a sophisticated supply chain attack. For roughly three hours, anyone who ran npm install pulled a backdoored version of a package they had trusted for years.
H2 → What Is Axios?
Axios is a promise-based HTTP client used in millions of JavaScript and Node.js applications. It simplifies making API requests — things like fetching data from a server or submitting a form. It is embedded in React apps, Vue projects, backend services, mobile apps built with React Native, and CI/CD pipelines across virtually every industry. At the time of the attack, it had over 100 million weekly downloads on npm.
H2 → How Did the Attack Happen?
The attacker did not find a bug in Axios's code. Instead, they targeted the human element — the maintainer's account.
The primary Axios maintainer's npm account (jasonsaayman) was hijacked. The attacker changed the registered email to an attacker-controlled ProtonMail address and gained full publishing access to the official Axios package on npm.
Within a 39-minute window, two poisoned versions were published:
[email protected]— tagged as the latest release[email protected]— tagged as the legacy release
Both release branches were hit simultaneously to maximize exposure across the ecosystem.
H2 → The Clever Part — A Hidden Dependency
The attacker never touched Axios's actual source code. Instead, they injected a fake dependency called [email protected] into the package.json of both poisoned releases.
This package was pre-staged 18 hours in advance. A clean decoy version ([email protected]) was published first to build a brief history on the registry and avoid "brand-new package" alarms from security scanners. Then the malicious 4.2.1 version followed.
When any developer or CI/CD system ran:
bash
npm install [email protected]npm automatically resolved the dependency tree, pulled [email protected], and executed its postinstall hook — a script called setup.js. That single execution was where the compromise began.
H2 → What Did the Malware Do?
The dropper used two layers of obfuscation — reversed Base64 encoding and an XOR cipher — to avoid static analysis tools.
Once executed, it immediately connected to the attacker's command-and-control (C2) server at sfrclak[.]com:8000 and downloaded platform-specific payloads:
Windows → PowerShell-based RAT
macOS → C++ RAT
Linux → Python-based RAT
All three were implementations of the same Remote Access Trojan — identical C2 protocol, command structure, and beacon behavior. The RAT gave attackers persistent, remote access to the compromised machine.
The malware then erased itself and replaced plain-crypto-js/package.json with a completely clean decoy. Running npm audit or manually inspecting node_modules after the fact showed no sign of compromise whatsoever.
H2 → What Data Was Stolen?
Any environment that installed the poisoned versions during the exposure window was at risk of losing:
Cloud credentials (AWS, GCP, Azure access keys)
SSH private keys
Kubernetes configuration files
CI/CD secrets and tokens
GitHub Actions tokens
Database passwords and API keys
Microsoft reported that attackers validated stolen credentials within hours using TruffleHog, then conducted reconnaissance across AWS services including IAM, EC2, Lambda, S3, and Secrets Manager.
H2 → Who Was Behind It?
Microsoft Threat Intelligence attributed this attack to Sapphire Sleet — a North Korean state-sponsored threat group focused on generating revenue for the North Korean regime. The group is also tracked by other vendors as BlueNoroff, CryptoCore, and STARDUST CHOLLIMA.
This attack was part of a larger campaign. Between March 19 and March 27, 2026, the same group had already compromised four other widely used open-source projects — the Trivy vulnerability scanner, the KICS infrastructure scanner, LiteLLM on PyPI, and the Telnyx library on PyPI.
H2 → Who Was Affected?
Anyone who ran npm install between 00:21 UTC and 03:30 UTC on March 31, 2026 and pulled a fresh copy of Axios was potentially compromised. This includes:
Developer workstations running manual installs
CI/CD pipelines with automatic dependency updates
Production systems rebuilt or redeployed during that window
Any project that depended on another package which depended on Axios (transitive dependency)
The malicious versions were live for approximately 3 hours before npm removed them.
H2 → Check If You Are Affected
Run these commands to inspect your environment:
bash
# Check installed Axios version
npm list axios
# Check if the malicious dependency exists
npm list plain-crypto-js
# Clear local npm cache
npm cache clean --forceAlso check your CI/CD pipeline logs for any npm install runs that may have pulled [email protected] or [email protected] during that window.
Look for outbound connections in your network traffic to:
sfrclak[.]comon port8000IP
142.11.206[.]72on port8000
H2 → What Should You Do Right Now?
1. Roll back to a safe version immediately:
bash
# For 1.x users
npm install [email protected]
# For 0.x users
npm install [email protected]2. Rotate all credentials — treat any machine that installed the bad versions as fully compromised. Rotate GitHub tokens, API keys, AWS credentials, SSH keys, and any other secrets accessible from that environment.
3. Flush caches and lockfiles:
bash
npm cache clean --force
# Delete node_modules and reinstall cleanly
rm -rf node_modules package-lock.json
npm install4. Review your CI/CD pipelines for any runs during the exposure window.
H2 → How to Protect Yourself From Future Attacks
Pin exact versions — avoid
^or~inpackage.jsonwhich allow auto-upgradesUse
npm ciinstead ofnpm installin CI/CD — it enforces lockfilesCommit your
package-lock.json— never.gitignoreitAudit postinstall scripts — be cautious of packages that run code on install
Enable dependency scanning tools like Snyk, Dependabot, or Socket in your repos
Adopt Trusted Publishing with OIDC to eliminate stored npm credentials
H2 → Conclusion
This attack is a textbook example of why supply chain security can no longer be an afterthought. The attacker did not break Axios's code — they broke the trust around it. One compromised npm account, one hidden dependency, and a 3-hour window was enough to put millions of developer environments at risk worldwide.
If there is one lesson here, it is this: the packages you trust are only as secure as the humans maintaining them.
Always pin your dependencies, always use lockfiles, and always have a credential rotation plan ready.
Tags: axios npm supply-chain-attack security malware RAT north-korea javascript cybersecurity developer-tools